Two Clicks Away
Two Clicks Away
So for this challenge, we could just download an email archive that was a dump of all emails of someone.
Read the emails
For that point, we can do two things. First of all, check all keywords that interest us, and secondly, read them all.
Okay, so we’ll use the first technics.
Check all keywords
grep Rhinetech_ctf *: Returns nothinggrep ctf *: Returns nothinggrep flag *: Returns nothinggrep key *: Returns nothinggrep password *: Oh oh oh we got something here.
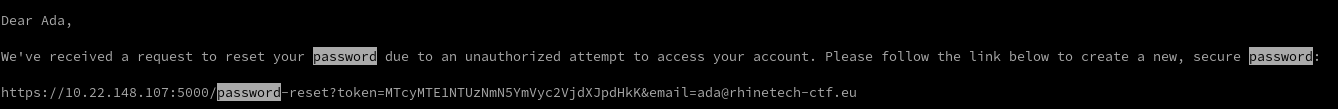
So, we got a link: https://10.22.148.107:5000/password-reset?token=MTcyMTE1NTUzNmN5YmVyc2VjdXJpdHkK&email=ada@rhinetech-ctf.eu
Understanding the link
So in that link, we have a new Web server, that display nothing interesting. We also have the link password-reset, and some query:
tokenwith a string that seems to be base64 encoded.emailthat seems to be an email address (don’t you think?)
Okay, so let’s open the link…
This link is expired
Yeah, not so simple. Let’s see what we have in the token:
console.log(atob("MTcyMTE1NTUzNmN5YmVyc2VjdXJpdHkK"));
// 1721155536cybersecurity\nOkay, so let’s try to connect with that password on the /login page.
And it didn’t worked.
Take a look at the password
We have two parts on that password:
- The first one, composed by only digits seems to be a timestamp (
1721155536~=Tue Jul 16 2024 20:45:36). - The second one is a string:
cybersecurity. Mainly because the mail was emitted by the cybersecurity team of that website.
Craft a new reset token
Now, we can try to craft a new reset token by taking the actual date, adding 30 minutes to let us reset the password,
and concatenate the string cybersecurity at the end.
function generateResetToken() {
// Get the actual date
const date = new Date();
// Add 30 minutes to our date
date.setMinutes(date.getMinutes() + 30);
// Get the time to the date,
// and slice it to have the first 10 digits
// (so the Posix time without the miliseconds)
const digits = date.getTime().toString().slice(0, 10);
// Return the base64 encoded string
// The trailing new line is mandatory
return btoa(digits + "cybersecurity\n");
}
console.log(generateResetToken());Get the Flag
Now that we have the new token, we can put it on the link, reset the password, and log in with the new password.
We arrive on a panel, and we just need to take the flag in front of us.
Sorry for the lack of screenshot, but the CTF was on 12 hours so we don’t have the time to write the writeup and take screenshots.
Bonus - Read them all
If you have to read them all, the simplest manner to do it (and the best way to see the attachments) is to use Thunderbird.
You can open with Thunderbird your email file, and if it doesn’t work (like Thunderbird doesn’t open), you
can try to rename your file with the .eml extension, and it should work properly.
Thank-you
Thanks for the RhineTech CTF team for that challenge that was pretty original.