Fake it till you make it
Forewords:
I’m not shure that the way I did it was the good one, but I’ll explain it to you.
Besides, I have my doubts, but the more I read the title of this challenge,
the more I’m convinced that I’m not a cheater.
Even though we were repeatedly told at the start of the CTF that brute force is “prohibited”
(It was not explicitly said for web challenge with that kind of attack because it’s on our computer,
but it was explicitly said for the reverse ones).
Challenge
On that challenge, we arrive on a page with two buttons: Login and Register.
On the register button, you have a long form that you don’t want to fill, trust me. So we’ll try to login (no time to register, I need to got the blood on that one).
Login
On the login page, we have a simple form with two fields: username and password.
As usual, I’m testing admin:admin, but it didn’t worked.
I also test: test:test in that case, and it worked. So let’s go.
We have a panel with the text: Welcome! You are now logged in. And a logout button.
Cookies
In the cookies, we have a JWT:
eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VybmFtZSI6InRlc3QiLCJpc19hZG1pbiI6ZmFsc2UsImV4cCI6MTczMjY1MzEzNH0.pDxue4VOF9Jv-O25k0iZ134JDWDdPQOX1sDO3dlKn5k:Ontopoftheworldmom
And thanks to jwt.io, we can decode it: The Header is:
{
"alg": "HS256",
"typ": "JWT"
}The body is:
{
"username": "test",
"is_admin": false,
"exp": 1732653134
}So the first thing I tried is to set the algorithm to none and just change my cookie.
But the website detected it, and I was logged out.
Hashcat
So, the next thing I tried, and I’m not shure it was a convinient way to do it. Maybe another way was possible, but I tried to crack the hash first, so don’t ban me please.
With hashcat, you can crack JWT token with the mode 16500.
In put my JWT token in a hash file, and I tried to crack it with the rockyou.txt wordlist.
hashcat hash -a 0 -m 16500 rockyou.txt
After less than a second, the password was cracked: Ontopoftheworldmom.
To be honest, it was so fast that I think it was the good way to do it, but I’m not shure that brute-forcing was the solution.
Probably an algorithm attack would work, but I didn’t try it.
Okay, so let’s change the JWT body, with the is_admin value to true.
After that, I was connected as admin, but nothing changed on the website.
DevTool
Unless … Yeah stupid guy, don’t pass 30 minutes on that challenge because you think you’re a genius, and you realize that the flag is not here, so you try all the values in your JWT instead of checking the source code of this beautiful page.
Please, open it. Right click, Inspect (Q). Please.
Control + Shift + I.
Please.
After complaining to myself, there is the solution:
- Open The DevTool of your favorite browser.
And there, just see by yourself:
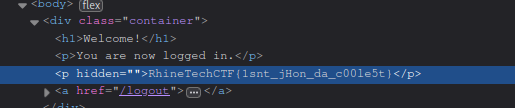
Do you see something? Are you shure?